Question
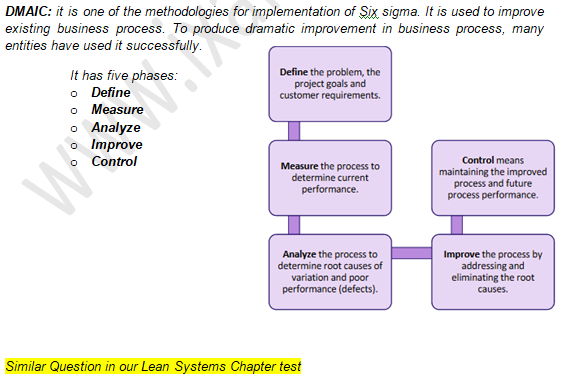
There are two methodologies for the implementation of
Six Sigma. Out of which one is DMAIC. Which of the following is not the correct expansion of the letters?Solution
Which of the following statements about Agrometeorology is correct?
Statement 1: Agrometeorology focuses on studying the relationship between wea...
If there is provision for only one irrigation, then at which stage in wheat the farmer should irrigate the crop?
Which one of the following is not a biological control agent:
Attraction of water molecules towards soil particles is:
The book, Historia naturalis was prepared by
The seed is born naked in
Which of following fruit is most suitable for jelly making
Ecology is the scientific study of the relationships between living organisms and their environment. Who first proposed the term "ecology"?
During the light-dependent reactions of photosynthesis, ATP and NADPH are produced in the:
Value of Correlation Co – efficient is



